NoScript Security Suite od Giorgio Maone
Dostupno u Firefoxu za Android™Dostupno u Firefoxu za Android™
The best security you can get in a web browser! Allow potentially malicious web content to run only from sites you trust. Protect yourself against XSS other web security exploits.
Za korištenje ovog proširenja trebat ćeš Firefox
Metapodaci proširenja
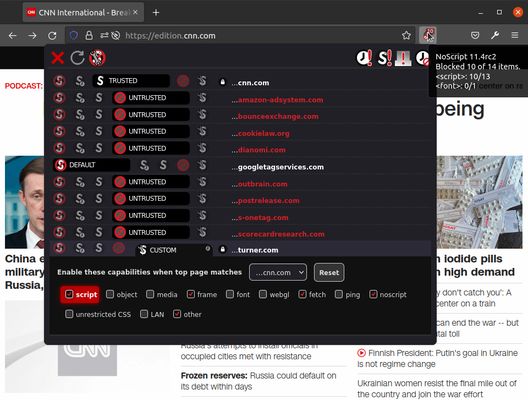
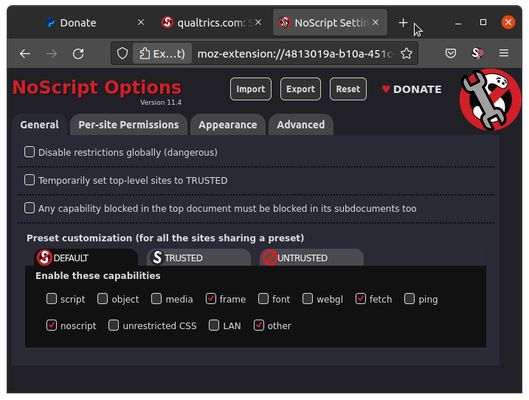
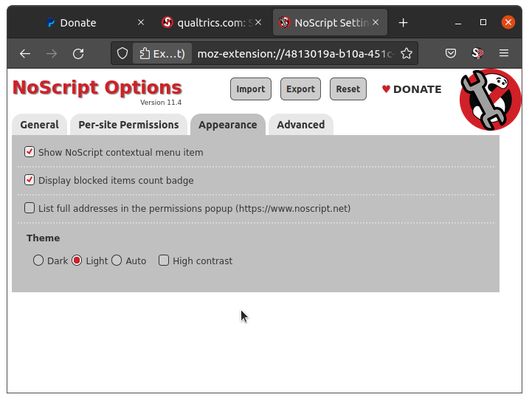
Snimke ekrana
Informacije o ovom proširenju
Winner of the "PC World - World Class Award" and bundled with the Tor Browser, NoScript gives you the best available protection on the web. It allows JavaScript, Flash, and other executable content to run only from trusted domains of your choice (e.g. your banking site), thus mitigating remotely exploitable vulnerabilities, such as Spectre and Meltdown.
It protects your "trust boundaries" against cross-site scripting attacks (XSS), cross-zone DNS rebinding / CSRF attacks (router hacking), and Clickjacking attempts, thanks to its unique ClearClick technology.
Such a preemptive approach prevents exploitation of security vulnerabilities (known and unknown!) with no loss of functionality where you need it.
Experts do agree: Firefox is really safer with NoScript!
FAQ: https://noscript.net/faq
Forum: https://noscript.net/forum
A Basic NoScript 10 Guide
Still confused by NoScript 10's new UI?
Check this user-contributed NoScript 10 primer.
and this NoScript 10 "Quantum" vs NoScript 5 "Classic" (or "Legacy") comparison.
It protects your "trust boundaries" against cross-site scripting attacks (XSS), cross-zone DNS rebinding / CSRF attacks (router hacking), and Clickjacking attempts, thanks to its unique ClearClick technology.
Such a preemptive approach prevents exploitation of security vulnerabilities (known and unknown!) with no loss of functionality where you need it.
Experts do agree: Firefox is really safer with NoScript!
FAQ: https://noscript.net/faq
Forum: https://noscript.net/forum
A Basic NoScript 10 Guide
Still confused by NoScript 10's new UI?
Check this user-contributed NoScript 10 primer.
and this NoScript 10 "Quantum" vs NoScript 5 "Classic" (or "Legacy") comparison.
Security issues affecting Firefox or the Tor Browser which can be fixed by a NoScript update are guaranteed to be addressed within 24 hours. This sometimes requires many updates to be issued in a short timespan, and when this happens you may notice NoScript UI's asking to "reload this page in order to operate properly". This is normal on "live" updates, and it just means the UI is out of sync with the page content, but there's no need to worry as all the restrictions to scripts and active content are still in place.
Ocijeni svoje iskustvo
Podrži ovog programera
Programer ovog proširenja te moli, da pomoću male donacije podržiš daljnji razvoj proširenja.
Permissions and dataSaznaj više
Potrebne dozvole:
- Pristupiti karticama preglednika
- Pristupiti aktivnostima preglednika tijekom navigacije
- Pristupiti tvojim podacima za sve web stranice
Daljnje informacije
- Poveznice dodatka
- Verzija
- 13.0.8
- Veličina
- 969,87 KB
- Zadnje aktualiziranje
- prije mjesec (20. svi. 2025)
- Povezane kategorije
- Licenca
- Samo GNU Opća javna licenca v2.0
- Politika privatnosti
- Pročitaj politiku privatnosti za ovaj dodatak
- Povijest verzija
- Oznake
Dodaj u zbirku
Napomene o izdanju za 13.0.8
v 13.0.8
x Reduce annoyances and false positives from sidebar content
detection (issue #444)
x Fix automatic top level trust conflict with existing
contextual policies (issue #441)
x Reduce annoyances and false positives from sidebar content
detection (issue #444)
x Fix automatic top level trust conflict with existing
contextual policies (issue #441)
Daljnja proširenja od Giorgio Maone
- Još nema ocjena
- Još nema ocjena
- Još nema ocjena
- Još nema ocjena
- Još nema ocjena
- Još nema ocjena